As cyber risks evolve, traditional security measures stagnate. Our innovative platform optimizes security configurations, enabling dynamic policy management across tools, bolstering defenses, and maximizing efficiency
Explore DiscernComprehensive dashboard, newsletters, cyber security tool report cards for CISO to share with various stakeholders
Curated actionable insights for CISOs
Change Identity, Endpoint, SASE settings automatically based on uncovered insights
Call the right SOAR playbooks, raise the right tickets on ServiceNow and make easy policy approvals on Slack
Dynamically tailor security to specific users/devices and entities based on risk with access to fine grained security settings
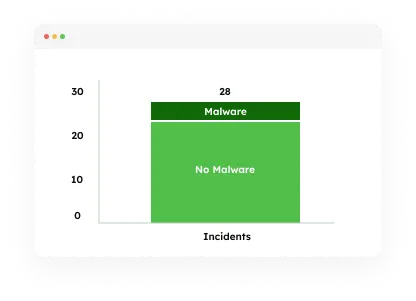
Progress reports and tangible ROI measurement with reduction in malware, phishing and targeted users.
Our compliance and threat assessment solutions are mapped to frameworks like MITRE ATT&CK® and D3FEND, NIST, CIS, and others to ensure that your security posture is dynamic and equipped to tackle the latest threats.
Provides a common language to understand and manage cyber threat
Helps decode attack cycle into TTPs commonly used by adversaries
Benchmarks against peers and relevant standards through actionable KPIs
Visualize endpoint health with our customized security configurations dashboard
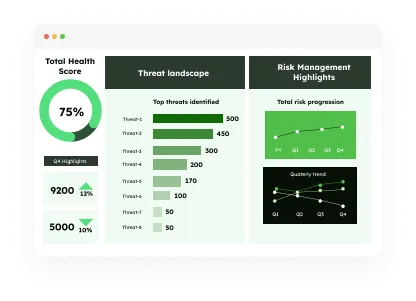
Know the most critical threats, vulnerabilities, and compliance issues across IT configurations and assets
Focus on the 5% of users, devices and assets that account for over 90% of the risk
Bolster your defenses with our closed loop policy automation approach across your array of security tool

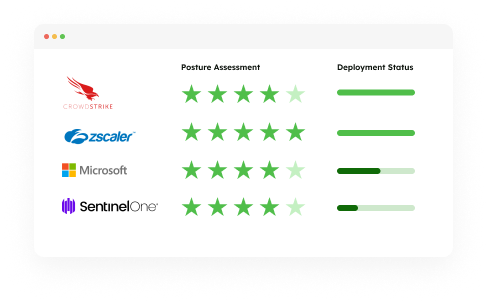
Discern the maturity of your security posture and cross-optimize security controls to prioritize the most critical gaps in configurations
1. Generate the most optimal pecking order for safeguarding your assets and security verticals
2. Create a culture of safety by gauging risk profiles of users
1. Leverage cost-benefit analysis of vulnerability remediation strategies
2. Improve incident response metrics through AI driven analysis of threat detection and response
1. Anticipate and preempt potential security risks through relevant KPIs
2. Track progress and inefficiencies through real-time scorecards
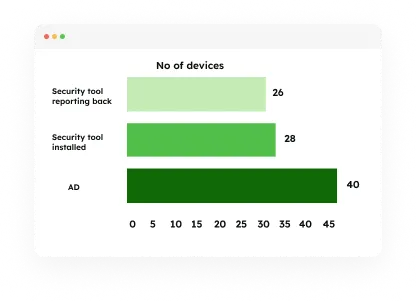
We start by establishing a baseline for your security controls and configurations through seamless integration with your entire suite of security products
Each of your security deployments undergoes a meticulous scoring process, evaluating both the effectiveness of controls and the associated risk factors.
Leveraging our advanced generative AI, we address your critical security queries, providing you with actionable insights and personalized configuration recommendations tailored to your department and target users
We dynamically map your security controls to established frameworks such as MITRE, CIS, and NIST, ensuring compliance. This not only showcases the progress of your security programs but also highlights their ROI
Our ongoing commitment includes performing regular health checks to ensure that your security controls remain current in the face of evolving ransomware threats. We also verify that you are leveraging the latest features offered by your vendors for enhanced security